How to identify malicious network traffic in wireshark
identify
How to detect network abuse with Wireshark
Timecodes:
No transcript (subtitles) available for this video...
Related queries:
how to identify malicious network traffic
examples of malicious network traffic
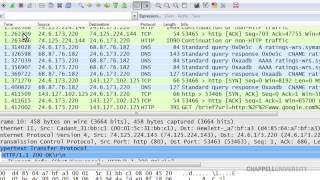
how to use wireshark to monitor network traffic
how to identify malicious packets in wireshark